Others
On the read receipts for PrivaSphere Registered Secure eMail™ and PrivaSphere™ eGov Registered Secure eMail you will find a QR tag printed.
With this tag it is easily possible to scan the meta data information from a achived paper print later on.
![]()
Example
<rM>
<d>Wed Mar 14 13:20:39 CET 2012</d>
<dt>0</dt>
<f>weber@privasphere.com</f>
<i>6</i>
<s>Wed Mar 14 13:13:06 CET 2012</s>
<t>tester4@email-revolution.ch</t>
<u>meinTitel</u>
</rM>
![]()
Legend
- t = to
- c = cc
- b = bcc
- z = size
- u = subject (max 40 chars)
- s = sending date
- i = dispatch mode integer
- 5: PrivaSphere Registered Secure eMail™
- 6: PrivaSphere™ eGov Registered Secure eMail
- d = delivery date
- dt = delivery type integer
- 0: read via WEB
- 2: delivery via encrypted email
- 3: blocked as spammer
- 5: delivered to archive
- 6: delivery via POP3
- 7: delivery via SMTP
- 11: registered mail refused
- 12: registered mail withdrawn after 7 days
- 13: delivered outside plattform
- 15: delivered via SOAP interface
- 16: delivered via encrypted PDF
- 17: delivered to other eGov platform
- 18: read on other eGov platform
- 19: eGov auto accept by authority
- 20: delivery via IMAP
- 21: delivery via asymmetric TLS
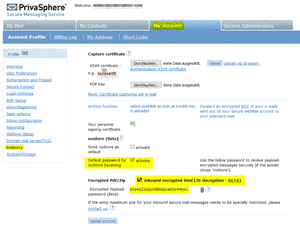
S/MIME encryption is one commonly seen approach for mail content encryption.
While it still reveals the relation of the involved parties and other message headers, it has the advantage to be usable End-to-End, i.e. from your personal device to your counterpart’s personal device.
In corporate contexts, this poses challenges to archival obligations, deputies resuming your tasks while you are ill, etc. Also, you might use multiple devices to read your mails – some of which may not have the technology to store decryption keys securely nor the functionality to decrypt or the device may simply not be cleared to read truly sensitive content (for example because it is a shared computer).
Therefore, true end-2-end S/Mime encryption is often complemented by gateway-based S/MIME encryption and signatures.
When using gateway based digital signatures, respondents might use the same certificate of you to encrypt replies.
If this happens infrequently, you might use the confidential PrivaSphere platform manually to decrypt single messages of that type for you.
If you want to use your gateway certificate regularly for response encryption in an external mail communication relationship, you might want PrivaSphere to automatically attempt to decrypt all inbound S/MIME encrypted messages addressed to you.
PrivaSphere’s Inbound Decryption Service will decrypt the gateway-certificate-encrypted message for you. You can either change your inbound DNS MX record to an extra PrivaSphere Host or you only relay decryption candidate messages to PrivaSphere.
Unless you have some other anti-spam/-virus service, you can combine this service with the excellent anti-SPAM service of our partner iWay.
Inbound signatures are furthermore scanned for certificates that can be used to send S/MIME encrypted messages to external recipients and are not known the confidential PrivaSphere platform yet. This ensures that you have the richest set of possible counterpart encryption certificates available to you.
If you also want outbound S/MIME encryption without the PrivaSphere standard of misrouting protection, please contact us to determine the set of issuers you trust to issue proper certificates not requiring bilateral end-user-peer authentication via MUC or alternative methods.
See also:
The EPFL security start-up "Di55erent" and PrivaSphere have put "swi5t" technology, with a patent pending in to BETA trial as a secure message delivery method.
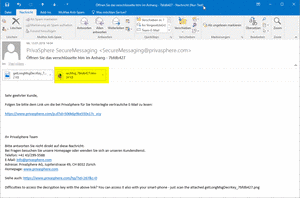
The attached encrypted html file is self extracting in nature - it opens up in a browser and upon entering the right password decrypts the file.
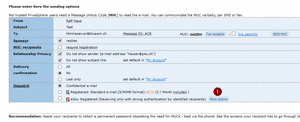
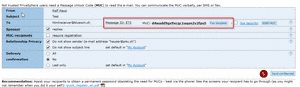
Four approaches to use this
a) Activate default reception as per screenshot
![]()
![]()
b) Alternatively use the "<encHtml>" subject tag (currently only in combination with <noStore>)
![]()
![]()
d) after sending: re-deliver as AES encrypted pushed html (or pdf) - in particular if the recipient can get e-Mail but not access the PrivaSphere website.
The sender needs to transmit the long key/MUC as sms/fax/Threema, etc.
![]()
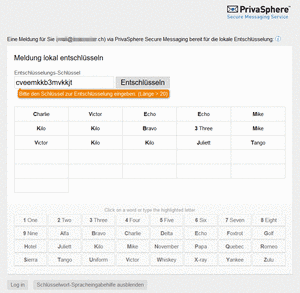
Receiving an encrypted HTML5 eMail:
The recipient will receive an email with an attached HTML file. This file opens locally with the browser.
In the opened file the user can log in the PrivaSphere account - the needed password will be received and filled in automatically.
![]()
Advantages:
1) It is completely browser based, requiring no installations, no certificates, etc.
2) The payload is transmitted only once and not up to 3 times or more as in other schemes.
3) The decryption of your message runs locally on your computer. No internet connection is needed for decryption.
4) After obtaining the decryption password once, you are no longer dependent on PrivaSphere being online/available
Limitations - " Di55erent " says:
<<A web browser able to handle HTML5 blobs. Common browsers support this feature since late 2012 or early 2013. Known to work are:
- Internet Explorer 10, 11
- Edge 12
- Firefox 13+
- Chrome 20+
Although Safari 6+ officially supports blobs, current versions have a serious issue that prevents decrypted files from being opened or stored to disk. >>
see also:
To send private confidential documents to employees such as salary reports, PrivaSphere offers a specialized function for clients with mail domain integration.
- Sends an additional notification mail about the receipt on a confidential mail to an individual personal email address
- Users can define the notification address in the PrivaSphere mail account
- All mails sent with the tag <salary> will not be delivered to the domain’s mail server (even no delivery via POP, SMIME/PGP, etc.)
- The mails marked with tag <salary> can only be read in the web interface
- The function “Further notification email salary” can be activated for domains by PrivaSphere
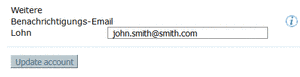
Insert your optional notification email address in your PrivaSphere Account:
- Log in your account
- Go to “My Account” – “User Preferences”
- Enter “Further notification email salary”
- Press “update account”
- A test message will be sent to this address
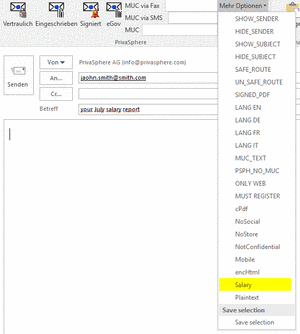
Sending “salary” emails:
- Use the subject tag <salary>
- Use the function in your outlook AddIn “More options” – “salary”
To enable this function please contact our sales team.
see also:
For security reasons, modern browsers do not prefill File-Upload paths into "Browse" Buttons because that could be used as a method to steal arbitrary files from a victim's computer.
See the detailed discussion e.g. for firefox under
See also:
If the PrivaSphere platform has SMIME encryption certificates available, it is possible to encrypt outgoing e-mails to the sender's domain.
The certificates can be automatically "harvested" from incoming eMails and used according the domain specifications.
(in preparation)
For specific domains there is the possibility of an LDAP query and thus the end-to-end encryption using SMIME certificates.
Currently, the certificates can be searched from the directory of the TeleTrusT European Bridge CA.
Enter an eMail address in your PrivaSphere account as a new contact - after a request by saving, an available certificate can be added to the contact and can be used for encryption.
Furthermore you can find the public keys of selected employees of the Swiss government as per https://www.staatskalender.admin.ch or http://www.bit.admin.ch/glossar/index.html?action=id&id=148
Should you know additional LDAP services with relevant public keys (incl. lists of the domains), please contact us.
A sender sends a secure message to you.
Please follow the link in the notification message to get access to this message:
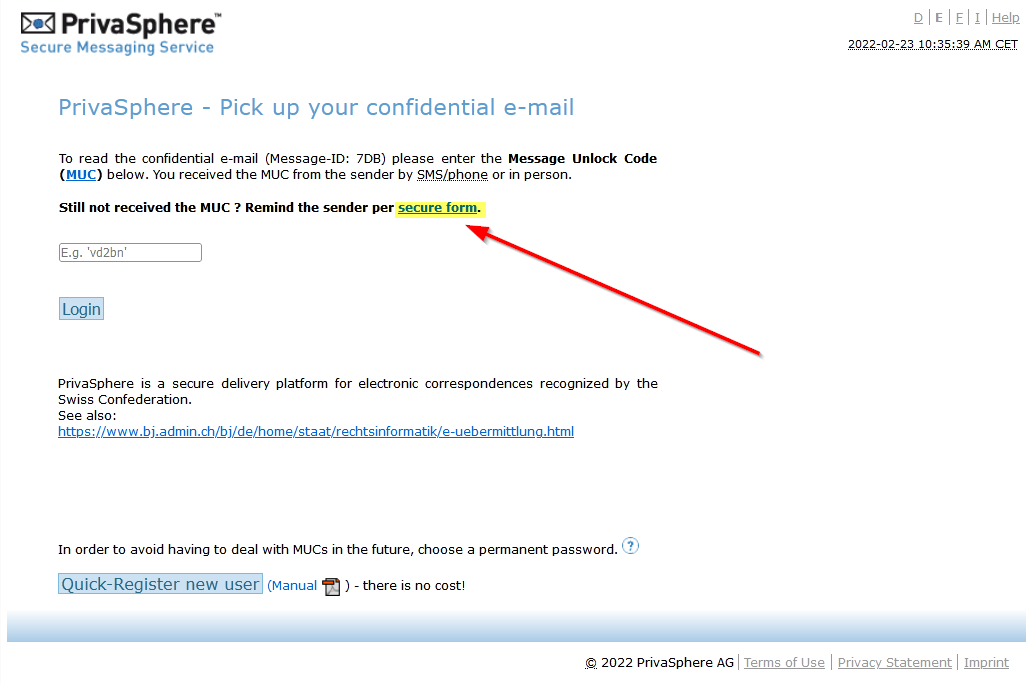
Here you are asked to enter the one-time password MUC (Message Unlock Code (1)). This MUC should be sent to you personally by the sender (via SMS / Fax / Tel ...).
If you have not received the MUC within a reasonable time, click on (2).
You can then leave a reminder to the sender.